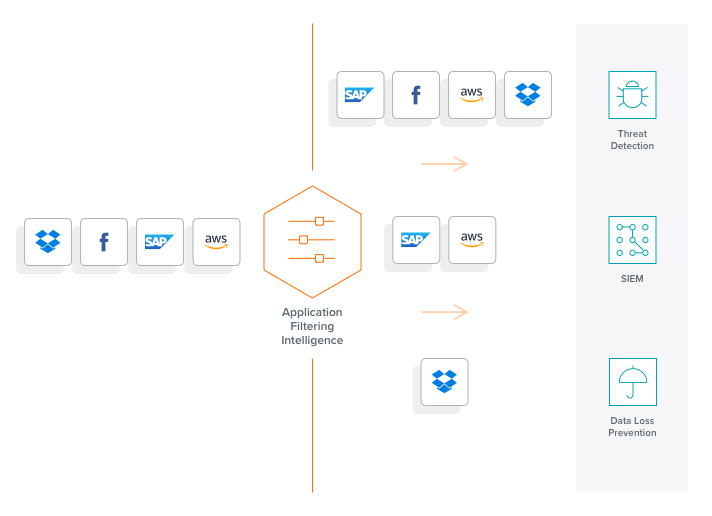
Application Identification and Traffic Forwarding
Gigamon Application Filtering Intelligence, a key component of Gigamon Application Intelligence, extends Layer 7 visibility to thousands of common and proprietary applications.
How Application Filtering works
Application Filtering Intelligence first identifies all the applications running on your network. Then, it lets you apply application filtering by using simple flow control to direct traffic by application, or families of applications only to the tools that require it. Irrelevant application traffic is not forwarded, saving storage and processing resources.
- Gain full visibility to the applications on your network along with the network resources they consume
- Increase tool efficiency and capacity — up to 80 percent in certain cases
- Improve network security by freeing up tool resources to protect a larger attack surface, including East-West traffic
- Decrease time manually analyzing network data with automatic application identification and isolation.
Full Application Visibility and Control
Gigamon Application Filtering Intelligence gives you end-to-end granular application visibility and the power to direct specific application traffic to the appropriate tools.
With application awareness and Flow Mapping®, NetOps and InfoSec teams can optimize network and security resources. Use cases include:
- Forwarding high-risk applications, such as CRM, Microsoft Office and BitTorrent search engine traffic, to intrusion detection systems (IDS).
- Identifying 5G mobile smartphone applications using SMS, MMS, IM, WAP and peer-to-peer, being transmitted by the GPRS Tunneling Protocol.
- Filtering out high-volume, low-risk web and video traffic, such as from Netflix and Hulu.
- Offloading routine maintenance and patches (such as Microsoft Windows updates) so they don’t bog down monitoring and security appliances.
Improved Efficiency of
Tools
Improves system performance by sending only applicable traffic to the right network and security tools at the right time.
Higher Security
ROI
By freeing up security resources, you can secure more of your network without additional investments.
Reduced Workload
for IT
Set and change application filtering policies with a few clicks — no more tedious scripting and updating rules.
Application Filtering Intelligence
Application Filtering Intelligence with Gigamon
Optimize Your Network Across Layers
“Improving observability is a critical challenge in network operations. Automating application identification and directing analysis traffic on that enhanced context is a powerful capability that Gigamon Application Intelligence brings to network management.”
GigaSMART Features
GigaSMART® offers a number of other essential traffic intelligence services required for active visibility into infrastructure blind spots, including:
NetFlow Generation
Delivering basic Layer 2–4 network traffic data to analysis tools.
Advanced Flow Slicing
Eliminates these issues by slicing payloads and packets from long data flow.
Source Port Labeling
Provides context to packets and allows tools to properly assess network behavior and threats based on where they are.
Adaptive Packet Filtering
Identifies patterns across any part of the network packet, including the packet payload.
SSL/TLS Decryption
Creates a secure channel between the server and the end user's computer or other devices as they exchange information.
Packet Slicing
Truncates packets while preserving the portion of the packet (the protocol headers) required for network analysis.
Advanced Load Balancing
Divides and distributes traffic among multiple tools, so network and security visibility can scale.
De-duplication
Targets, identifies and eliminates duplicate packets, blocking unnecessary duplication and sending optimized flows.
Masking
Provides customizable data protection by overwriting specific packet fields with a set pattern.
Tunneling
Alleviates blindness of business-critical traffic at remote sites, virtualized data centers, or hosted in a public cloud.
Application Visualization
Provides a complete view of the applications running on your network automatically.
Application Filtering Intelligence
Extends Layer 7 visibility to thousands of common and proprietary applications.
Application Metadata Intelligence
Empowers your security information and event management and network performance monitoring tools.
GTP Correlation
Enables mobile service providers to monitor subscriber data in GPRS Tunneling Protocol tunnels.
5G Correlation
Intelligently forward subscriber sessions to specific tools by filtering on subscriber, user device, RAN or network slice IDs.
FlowVUE Flow Sampling
Provides subscriber IP-based flow sampling.
SIP/RTP Correlation
Enables enterprises and service providers to monitor VoIP traffic.
Have Questions?
We're here to help you find the right application visibility solution for your business.
By submitting this form, you agree to our Terms & Agreement. View our Privacy Statement.